Organizations have employed contactless physical access control for decades and, like any other technology, it has improved over time. From antiquated magnetic swipe technologies to low frequency contactless, to high frequency contactless and mobile, there is a variety of access control technologies with varying degrees of security in use today. Knowing the vulnerabilities to each is critically important when it comes to handling identity data and credentials.
Despite the enhanced security that comes from newer options, many organizations are still using outdated and vulnerable credential technology. For these organizations, the time has come to re-evaluate their risk profile and prioritize plans for a much-needed upgrade. Continued use of outdated credentials with known vulnerabilities puts organizations at much higher risk of identity data theft, cloning, spoofing and potential breach.
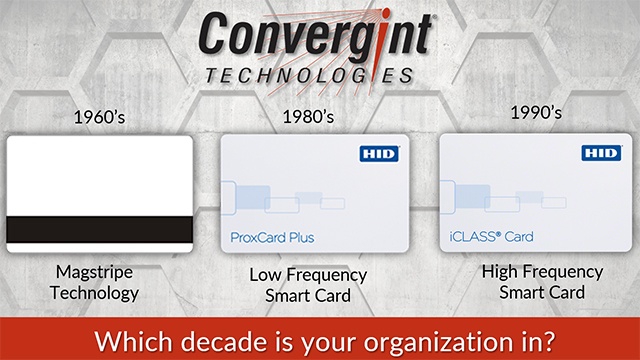
To better illustrate the importance of upgrading to the latest technology, here is a visual illustration of the evolution of access control credential technology.
Which decade is your organization in?
1960s
Unencrypted Magnetic
Stripe Technology

Early form of data storage on a magnetic stripe
1980s
Unencrypted Memory
Chip
Data storage inside a card on a memory chip
1990s
High Frequency
Smart Card
Expanded memory for data storage inside a card on a memory chip
If an organization is employing any of the technology shown above, it’s time for an upgrade. Convergint, partnered with HID Global, will help develop and implement a customized path to higher security. Next generation Seos® credential technology not only brings organizations up to the current industry standard but takes trusted identity management beyond the door and into the future.
Seos High Security Access Credentials
Seos credential technology has advanced encryption and a software-based infrastructure that enables identity data to be securely placed on a variety of form factors, including mobile devices.
Strict adherence to best practices for data protection and widely reviewed open standards ensure excellence in design. Its unique, layered security approach to key management, mutual authentication, secure messaging ensures a high degree of data privacy and security.
Examples of the best practices followed by Seos technology includes:
Need some help to “get with the times”? Convergint and HID Global can help your organization upgrade to the industry standard for access control, reduce risk, and position secure identity for the future applications.