There are over 55,000 substations in the U.S., many of which are enticing targets due to the important function they perform and the fact that they are typically unstaffed in remote settings.
Traditionally, electrical substation security was focused only on preventing unauthorized access, to stop vandalism and improve safety. But today, security efforts have been redefined to address new threats to protect critical infrastructure. Substations are vital elements in the distribution of high-voltage electrical networks, and any disruption can have a severe impact on society. Together these new threats bring government mandates that drive more security implementations.
Several years ago, the North American Electric Reliability Corporation (NERC) told U.S. energy producers to do a better job of securing energy stations. To comply with the NERC security requirements, utility companies are seeking more robust ways to secure critical locations that often have few attendant personnel.
In the past, the electrical grid operated with mechanisms that relied on physical or manual resources, but modern systems are interoperable networks of control and data acquisition. Electrical generation, a foundation of modern convenience that contributes significantly to a higher quality of daily life, has become a critical component of practical and economic stability—and therefore a major focus in national security because it is vulnerable to acts of terrorism. The challenges can be daunting. Fortunately, there are technologies available to assist utilities in their compliance with these requirements.
The Zone Approach to Securing Critical Infrastructure
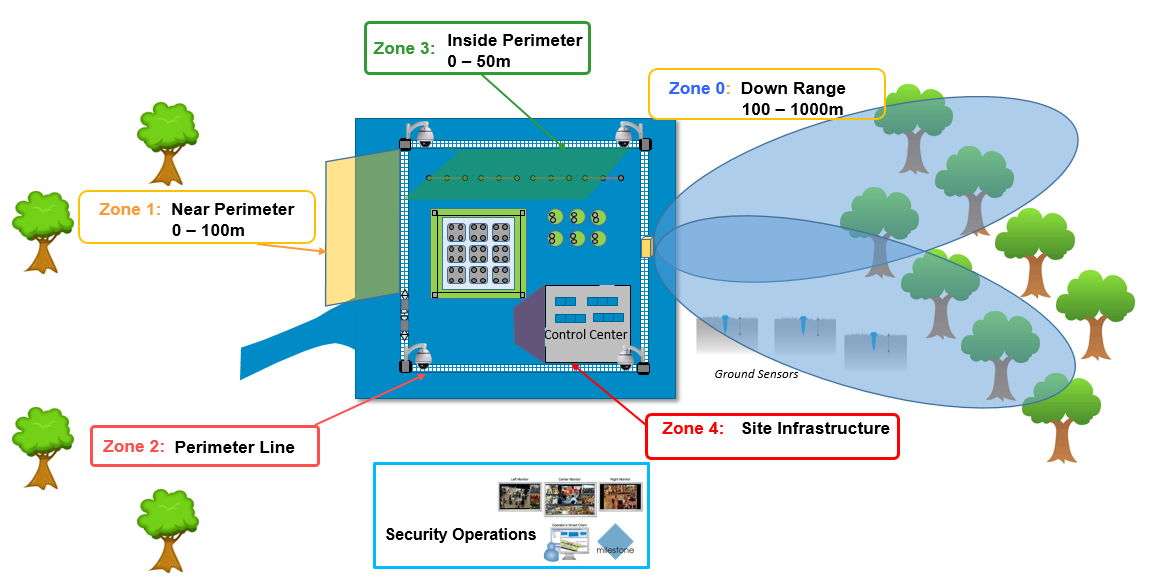
The best way to approach modern physical security installations for electrical generation and substations is to conceptualize the facility as having different zones, with the perimeter being the first line of defense. Different technologies can be applied for each zone, which are then tied together through an integrated network with video verification.
A successful security strategy makes sure that all physical aspects of a security system—cameras, remote and mobile monitoring applications, access control systems, networks, intercoms, emergency exits, perimeter sensors, lighting, and all other safety aids—are installed properly and fully functional. Within the zones of a security plan, the total solution is only as strong as the weakest point.
Deploy with Unifying Open Platform Video
Dividing the property into different zones allows optimum detection elements for each zone. It’s important to develop a system based on an open platform technology that is designed to interconnect different components from a variety of vendors. No single vendor has all the pieces to the puzzle, so it is good best practice to be future-ready for new capabilities that are continually coming to market.
Easily search, source, and learn about the many applications, hardware and services possible with an open-platform VMS. The Milestone Marketplace includes solutions verified by Milestone Systems to be compatible with the XProtect software platform. Convergint is a long-time Milestone partner with deep expertise in these technologies and how to integrate them optimally.

